Information is one of the most valuable assets any organisation can consider an important factor of a business goals and growth. Due to this, its integrity and confidentiality can have a direct effect on day-to-day business life, and can cause irreversible damage if it is disclosed or breached.

Nowadays, various tech companies release applications and algorithms to encrypt data, and ensure they can provide powerful methods to lock down access to sensitive information. Although using proper methodology and technology to protect information is the main part of the information protection process, classifying the data and rating them based on their security sensitivity is the first step.
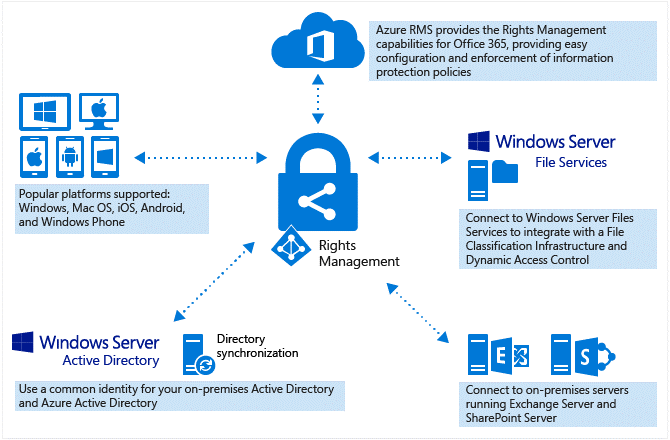
Azure Right Management Services (RMS) is a cloud-based technology by Microsoft, which is used by Azure Information Protection. Azure RMS has more features and capabilities compared to Active Directory RMS (AD RMS), which was introduced many years ago. This service uses identity, encryption, and authorisation policies (or data access policies) to secure the emails and files of an organisation located on the cloud, or on-premises servers. As a cloud based service, there is no limitation to the type of devices or operation systems (OS) that can be used on the mobile devices when trying to access to the protected emails and files. As a result, RMS supports Windows, Mac OS, iOS, Android, and Windows Phone (Microsoft’s Enterprise Mobility + Security suite (EM+S), a comprehensive mobile device management tool using Azure Information Protection).
The persistent protection that Azure RMS provides not only helps secure your company data, but might also be legally mandated for compliance, legal discovery requirements, or simply for good information management practices. The main vital difference between Azure RMS, and other information protection solutions using peer-to-peer encryption, is that Azure RMS still allows authorised people or search/indexing services to read and inspect protected data, something not easily achievable with other solutions.
Let’s cover a couple of important requirements and problems that can be met and resolved by using Azure RMS.
Safely share information

When users share a protected file, they can be confident that only authorised people can access files attached to an email or a stored file on a SharePoint shared link. Users can also protect the entire email message if it includes sensitive information inside the email body, as well as allowing them to activate the “Do Not Forward” option form in Outlook. In this way, even the recipient forwarding the email to someone else means that the email or attached files cannot be read beyond the initial recipient.
Auditing and Monitoring

Organisations can audit and monitor the usage of protected data. This is not limited to the files kept inside the organisation. If company X shares a protected file with company Y (for example, if they’re working on the same project and need to share information with read-only permissions), the auditing and monitoring features provide the following benefits:
- If allowed users in company Y opened the files, company X will be able to see if they did, and when.
- Company X are able to check audit logs to see if non-authorised users have tried to access any protected files (This can easily occur by forwarding emails with attachments or saving protected files inside shared folders, accessible by external users).
- Company X will quickly be notified if protected files with read-only permissions have had modification attempts or have been printed.
- Company X will also be able to tracking and revoke access to shared files and generate reports of how the files were shared, and who accessed the files.
Support for business-to-business collaboration

With RMS, it’s not necessary to configure a trustworthy way of working with other organisations before sharing protected files. If another organisation uses Office 365 or an Azure AD Directory, the collaboration between your company and theirs is automatically supported. In addition, if another organisation is not using either of those platforms, they can sign up for RMS using an individual subscription for free, or alternatively use a Microsoft account for applications that support this type of authentication for Azure Information Protection.
Support for on-premises services, as well as Office 365

Azure RMS can be used by on-premises services such as Exchange Server, SharePoint Server, and Windows servers running the File Classification Service (File Servers). There’s no doubt that Office 365 services can and do work seamlessly with Azure RMS.
Ability to scale across your organisation, as needed

As Azure RMS is a cloud based service, it automatically scales up and out, so your company doesn’t need to deploy more servers to cover the additional workload. So scale the information protection across your organisation easily, and take advantage of enjoying a protected shared environment, both internally and externally.
In the next few articles, I will cover how to take advantage of implementing this technology for different services, taking you through step-by-step implementation processes for various popular services.
By Pouya Koushandehfar, Subject Matter Expert
If you are looking for flexibility, scalability and cost control in a secure cloud environment, contact us at info@byte.com.au or give us a call at +61 3 9828 9999.



